CIA stands for Confidentiality, Integrity, and Availability and no, we’re not talking about secret agents (though cybersecurity does have its own brand of espionage). These three principles form the absolute cornerstones of the entire cybersecurity industry, acting as the universal measuring stick against which every single threat is assessed and rated for criticality. Like three judges on a panel, each scoring how dangerous a threat really is. On the blue teaming side of things, achieving a High CIA rating is the gold standard, it means your systems are considered safe, solid, and properly hardened against whatever the adversaries might throw your way.
CIA TRAID
1. CONFIDENTIALITY
Confidentiality is exactly what it sounds like, it’s all about how well you can keep a secret, or more precisely, how well you can ensure that only the right people get to see the right things. Think of it as being a really good bouncer at an exclusive club; your job isn’t just to let the right people in, but equally to keep the wrong ones out.
In companies this selective control over who sees what, prevents accidental disclosure, unauthorized access, and at the extreme end of the spectrum, the outright theft of critical information, assets, or access credentials that could unravel everything.
2. INTEGRITY
Integrity is exactly what it sounds like too, it’s all about making sure that the information you’re looking at is the real deal, untouched and unaltered from the moment it was created to the moment it lands in front of you. Think of it as a wax seal on a royal letter; if that seal is broken or tampered with, you immediately know something fishy happened along the way.
In companies, this assurance that data hasn’t been quietly modified, corrupted, or maliciously manipulated is what keeps decisions trustworthy and systems reliable. Because at the extreme end of the spectrum, a silent tweak to a financial record, a forged transaction, or a backdoor edit to a configuration file could cause catastrophic damage and the scariest part is, you might not even notice until it’s far too late.
3. AVAILABILITY
Lastly, Availability is also exactly what it sounds, it’s all about making sure that the right people can get to the right information, at the right time, every single time they need it. Think of it as a 24/7 convenience store; it doesn’t matter how secure or well-stocked it is if the doors are locked every time a customer shows up.
In companies, this guarantee that systems, data, and resources are up, running, and accessible when needed is what keeps the business breathing. Because at the extreme end of the spectrum, a crashed server during a critical transaction, a ransomware attack locking everyone out, or even a poorly timed maintenance window could grind entire operations to a halt and in today’s always-on world, downtime doesn’t just cost money, it costs trust.
Why You Can’t Max Out the CIA Triad.
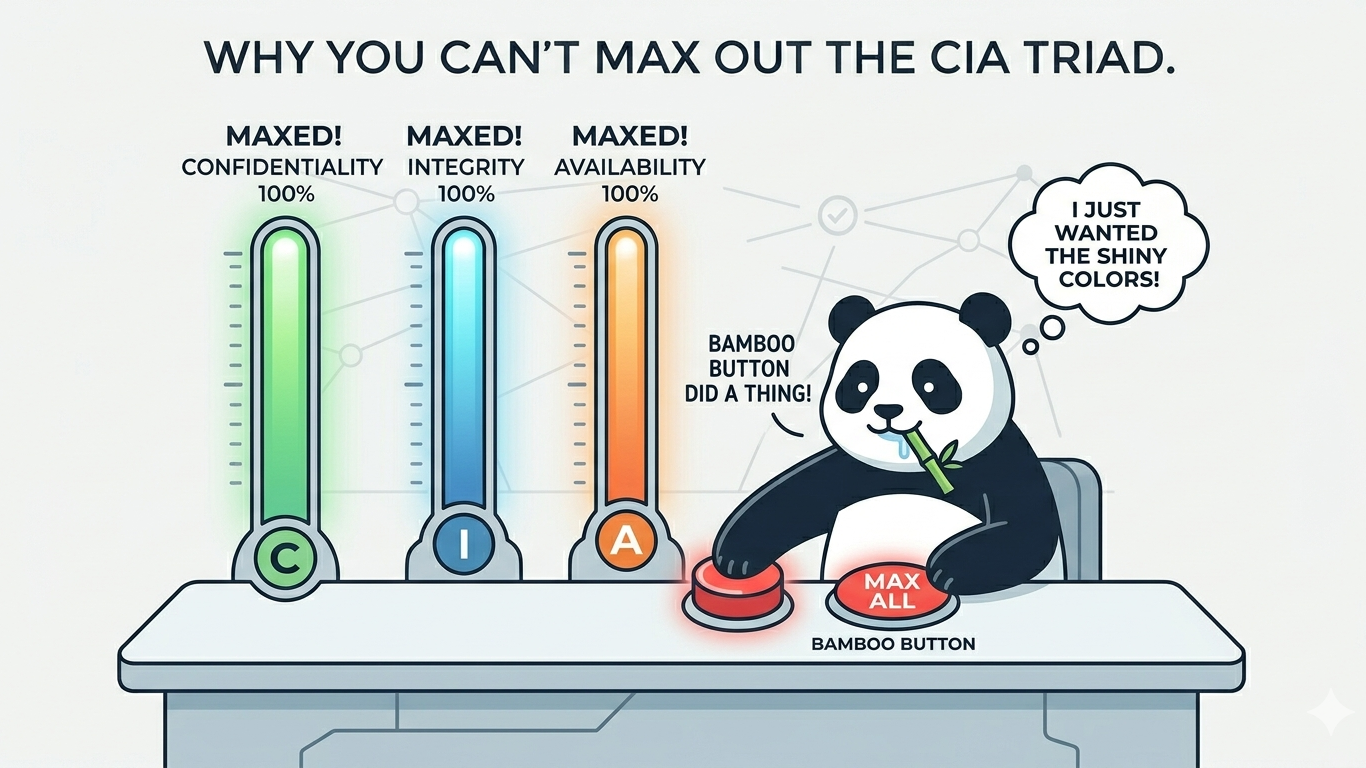
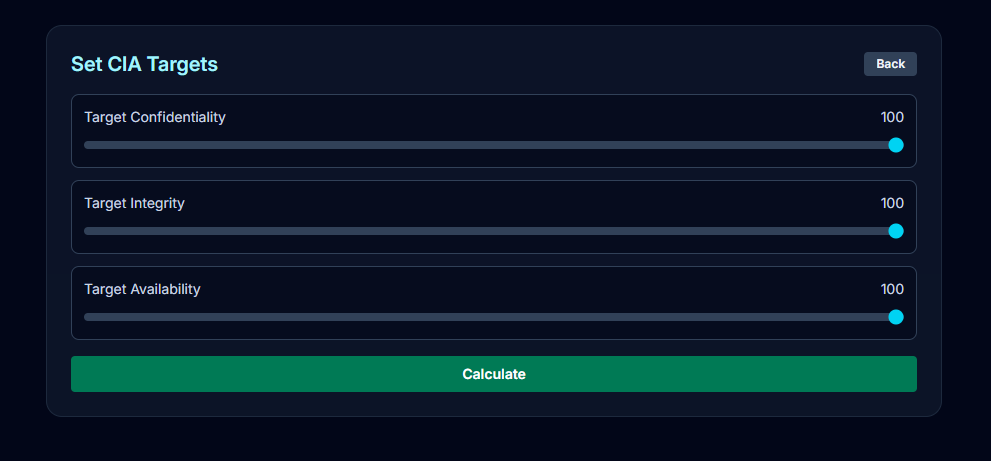
"If the CIA Triad is so important... then why don’t we just max it out and become unhackable?"As it turns out, “Maxing Out CIA” sounds like the dream move from a security standpoint and technically, it is. But push all three dials to the absolute maximum and you’ll quickly discover that what’s perfect for security can be a serious headache for business. To make this tradeoff tangible, I’ve built a simulator that demonstrates exactly how an over-hardened CIA posture can start working against the very organization it was meant to protect.
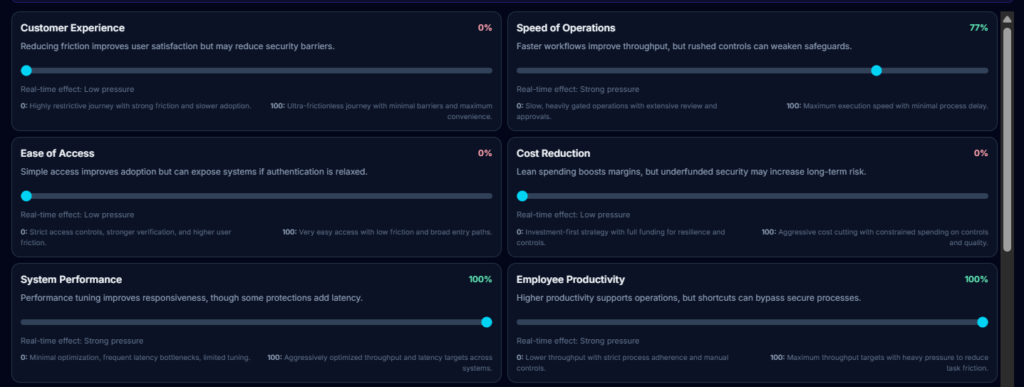
RESULTS
- Customer Experience (0%) : No Customer is having good time interacting with the business.
- Ease of Access (0%) : Access to anything is very strict and time consuming with lots of verifications.
- Cost Reduction (0%) : No scope of cost reduction for the business in terms of security.
- Rapid Deployment (0%) : Slow development process due to long validation and change windows.
- Operational Flexibility (0%) : Strict change control with formal review before every change
Going full security-mode and maxing out CIA brings the numbers to a perfect 100/100 with a Risk Level at 2/100, but at a devastating cost to the business. The fortress is impenetrable, but nobody wants to live in it.
Let’s Recalibrate: A Business-First Perspective
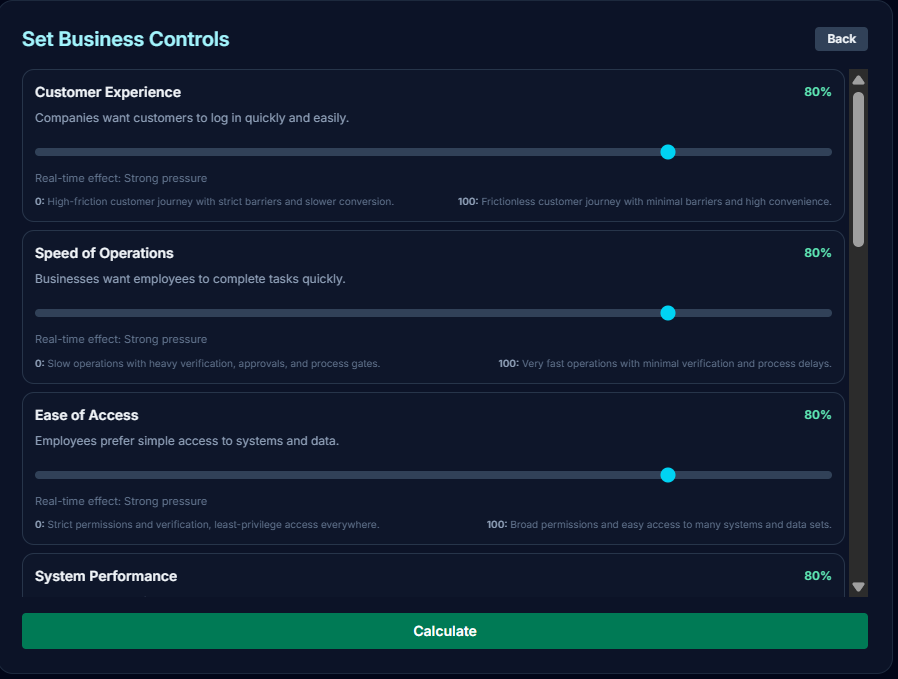
Inputs
- Customer Experience (80%) : Customer are having good time interacting with the business.
- Ease of Access (80%) : Access to anything is easy and intuitive.
- Cost Reduction (50%) : Some scope of cost reduction for the business in term of security.
- Rapid Deployment (80%) : Quick and agile development process short testing windows.
- Operational Flexibility (50%) : Moderate change control regulations, only focusing on big changes.
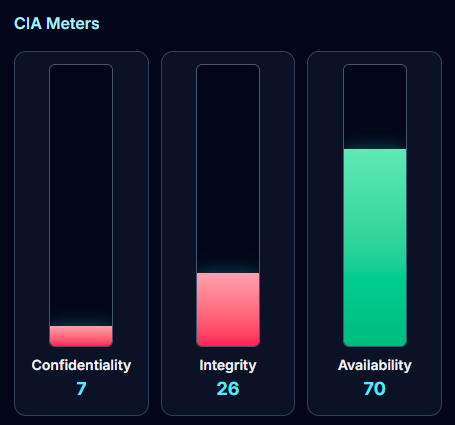
Swinging to the complete opposite extreme and going full business-first doesn’t work out either, and the numbers tell that story better than anything else. With Confidentiality sitting at a worrying 7/100, Integrity at 26/100, and Availability at 70/100, the overall Risk Level climbs to a concerning 70/100. That’s not a business-friendly setup, that’s just a security disaster waiting to happen with a smile on its face.
CONCLUSION
And that right there is the million-dollar tightrope act that every CXO walks every single day. Too much security and the business suffocates under its own defenses, too little and it becomes an open invitation for disaster which means the sweet spot isn’t at either extreme, it’s somewhere thoughtfully in the middle. This delicate balance between locking things down and keeping things moving is not just a technical decision, it’s a strategic one that shapes how a company operates, competes, and survives in an increasingly hostile digital landscape.
This is precisely why the conversation around CIA is never purely a security team’s conversation, it lives in boardrooms, budget meetings, and executive strategy sessions just as much as it does in SOC dashboards. CXOs aren’t just signing off on firewalls and access policies, they’re constantly negotiating the invisible contract between protecting the business and enabling it to grow. Every policy, every control, and every investment is a calculated bet on where that balance should sit on any given day.
At the end of it all, cybersecurity isn’t about building the highest wall possible, it’s about building the right wall, in the right place, without accidentally locking your own people out. And mastering that balance? That’s not just good security. That’s just good business.